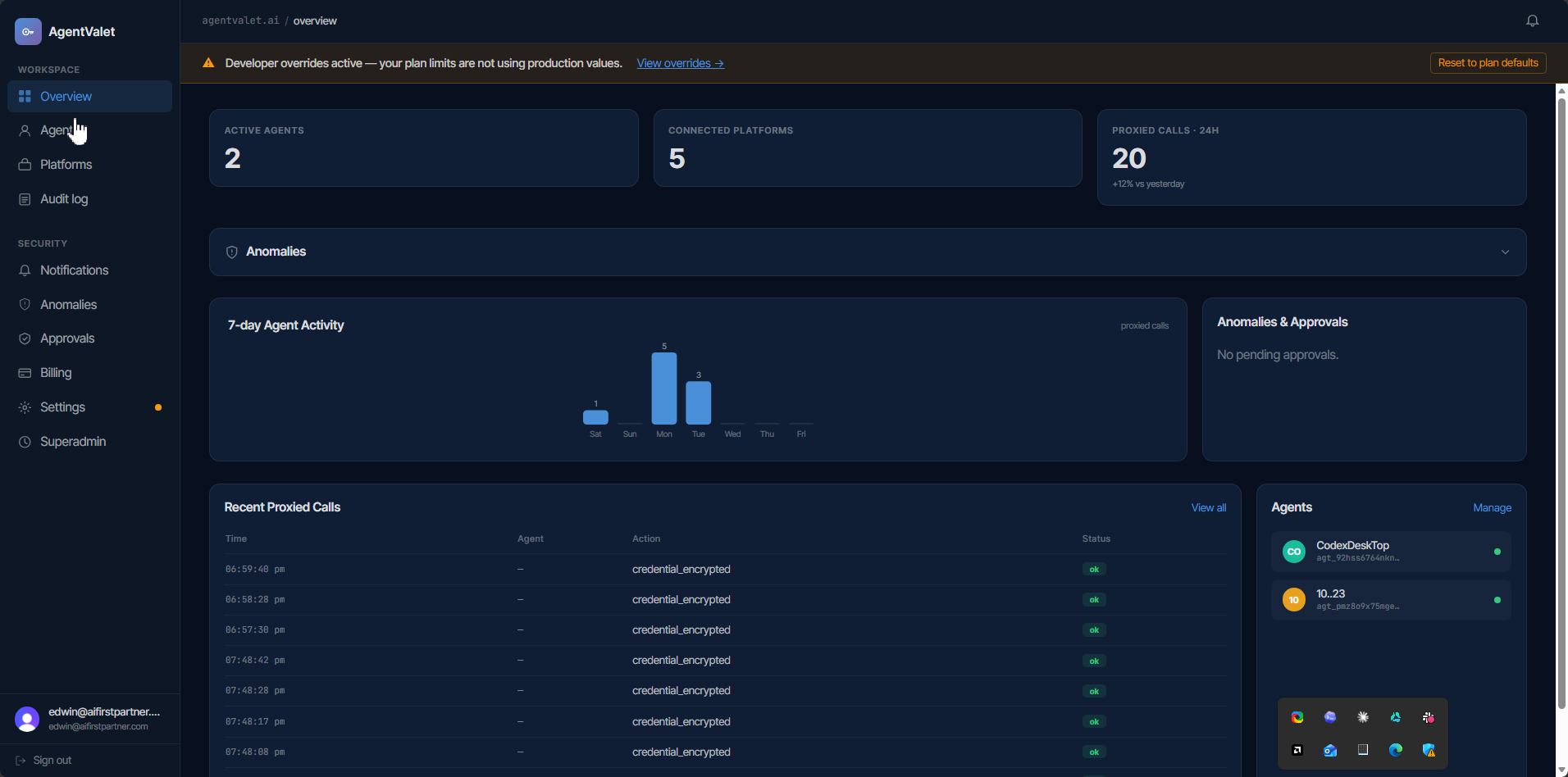
See what your agents are doing.
A single console for identity, permissions, platforms, and the audit trail. Built for owners who need to know - and prove - what every agent did.
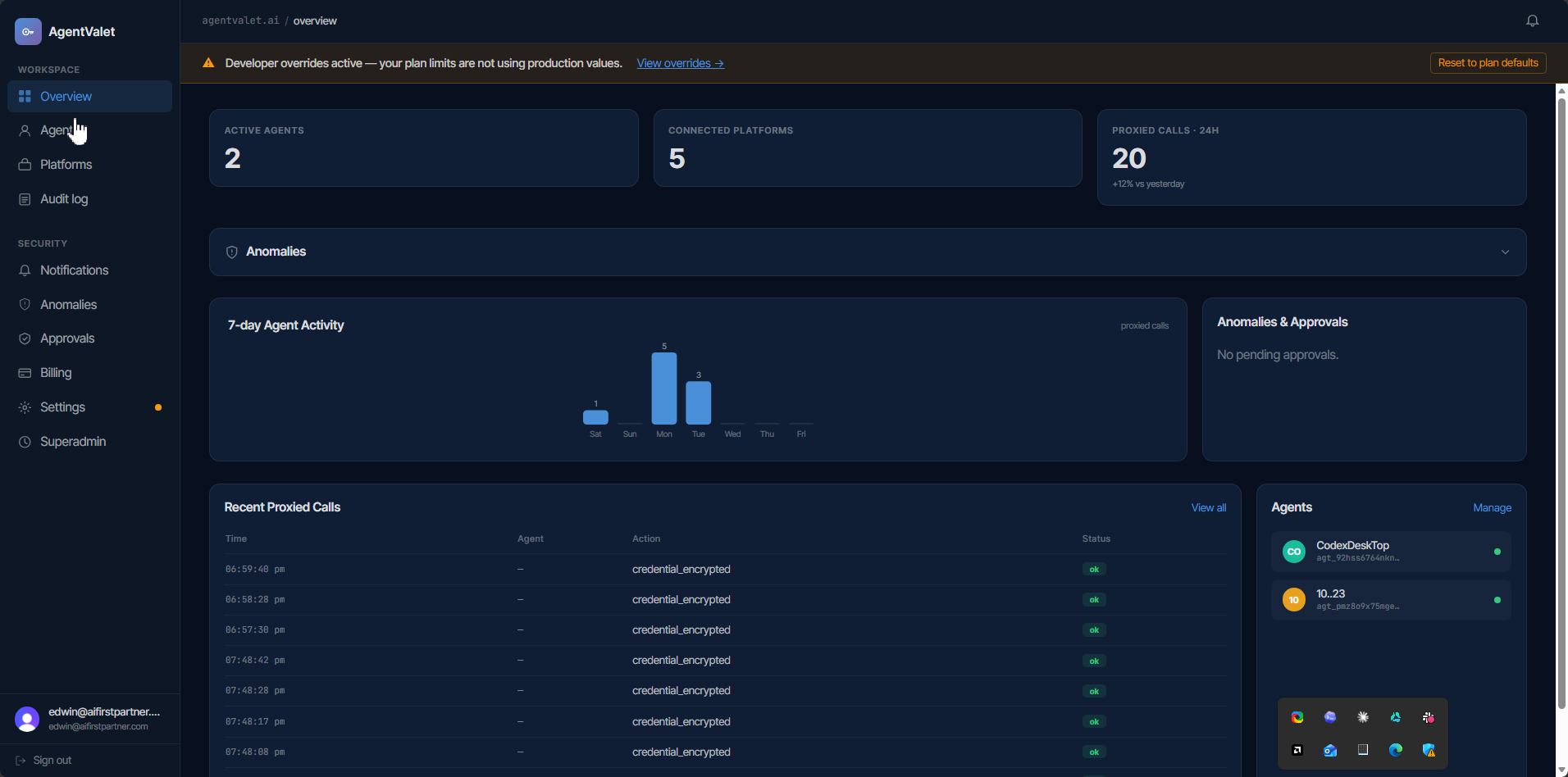
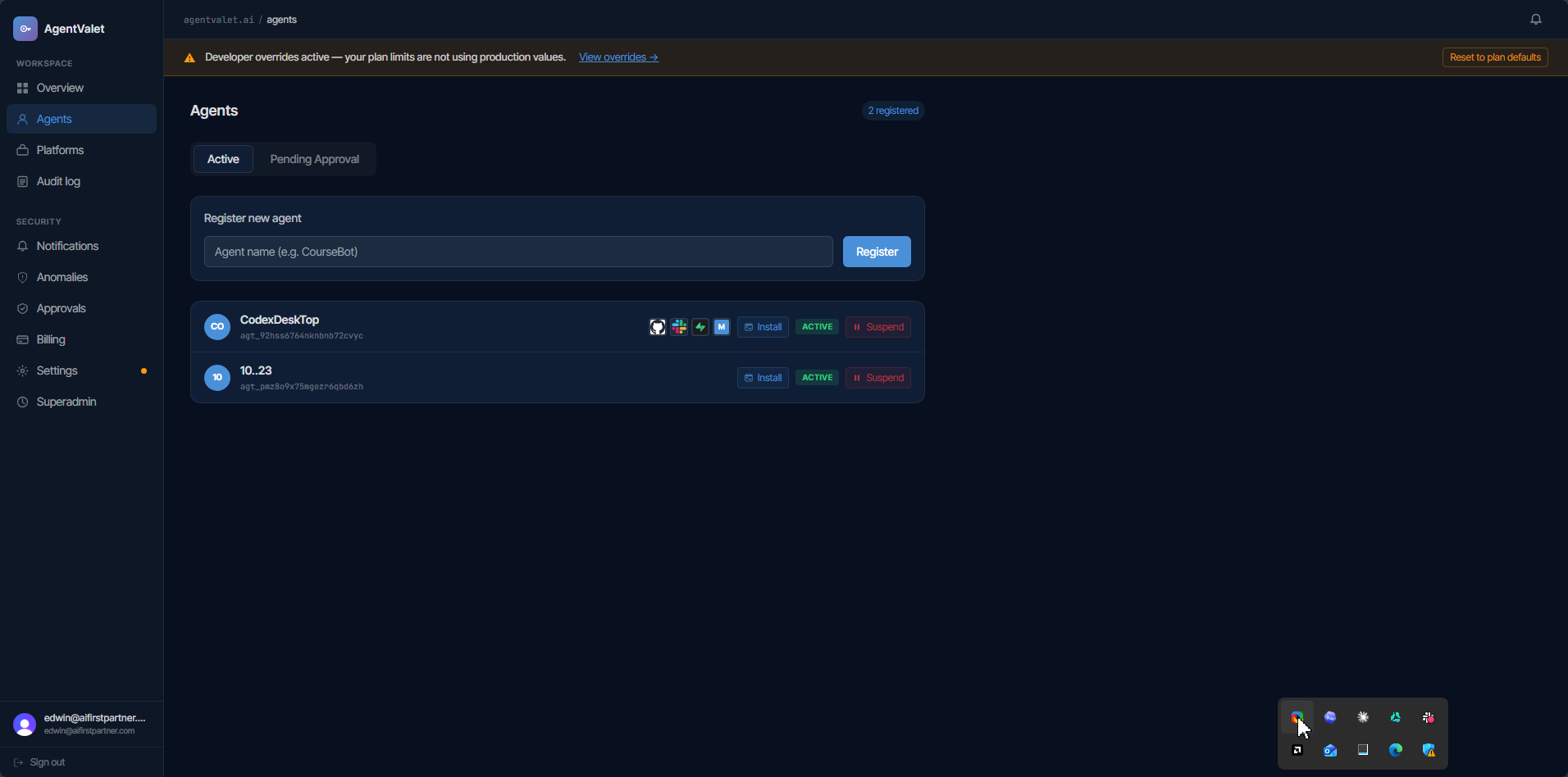
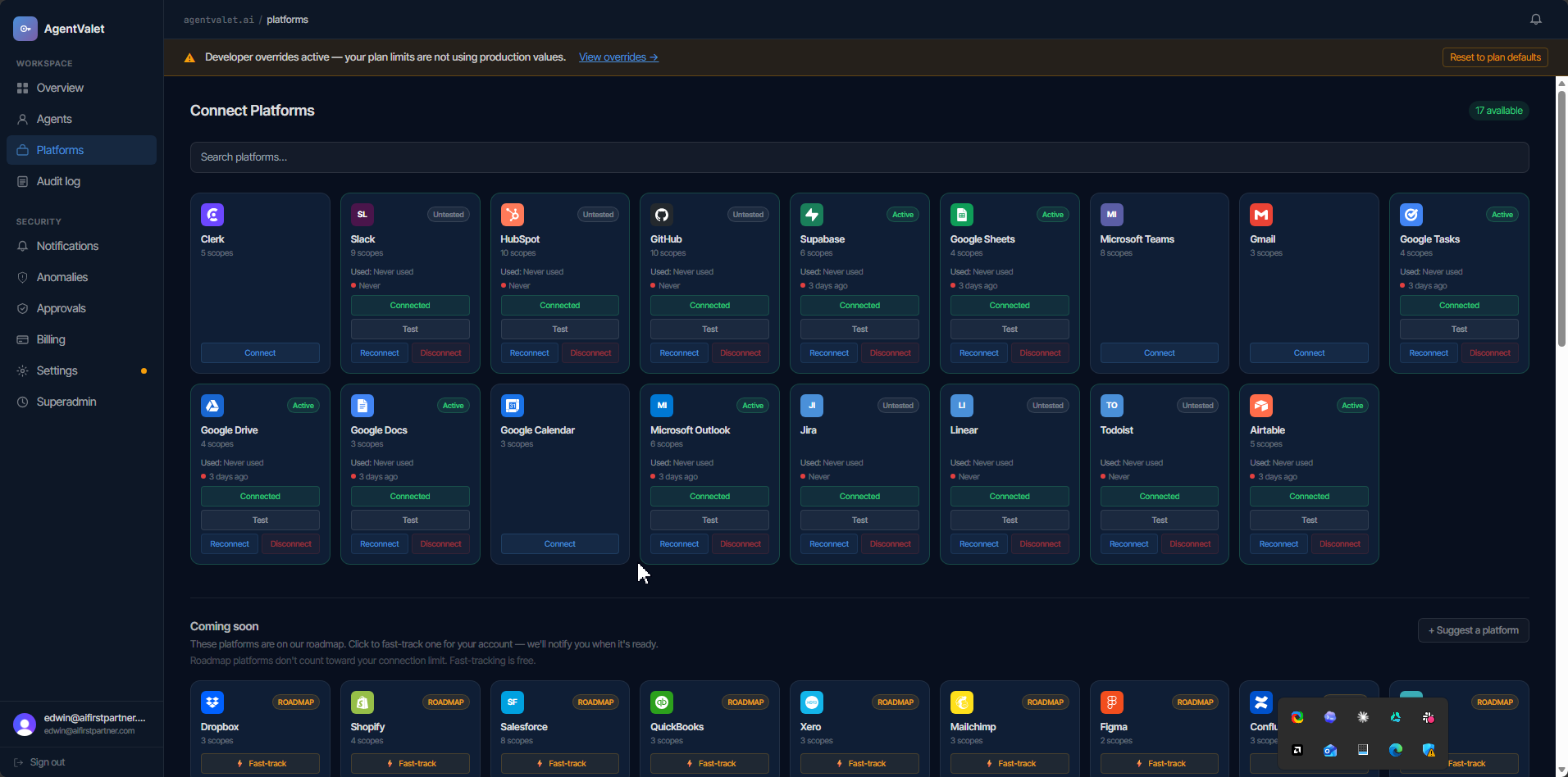
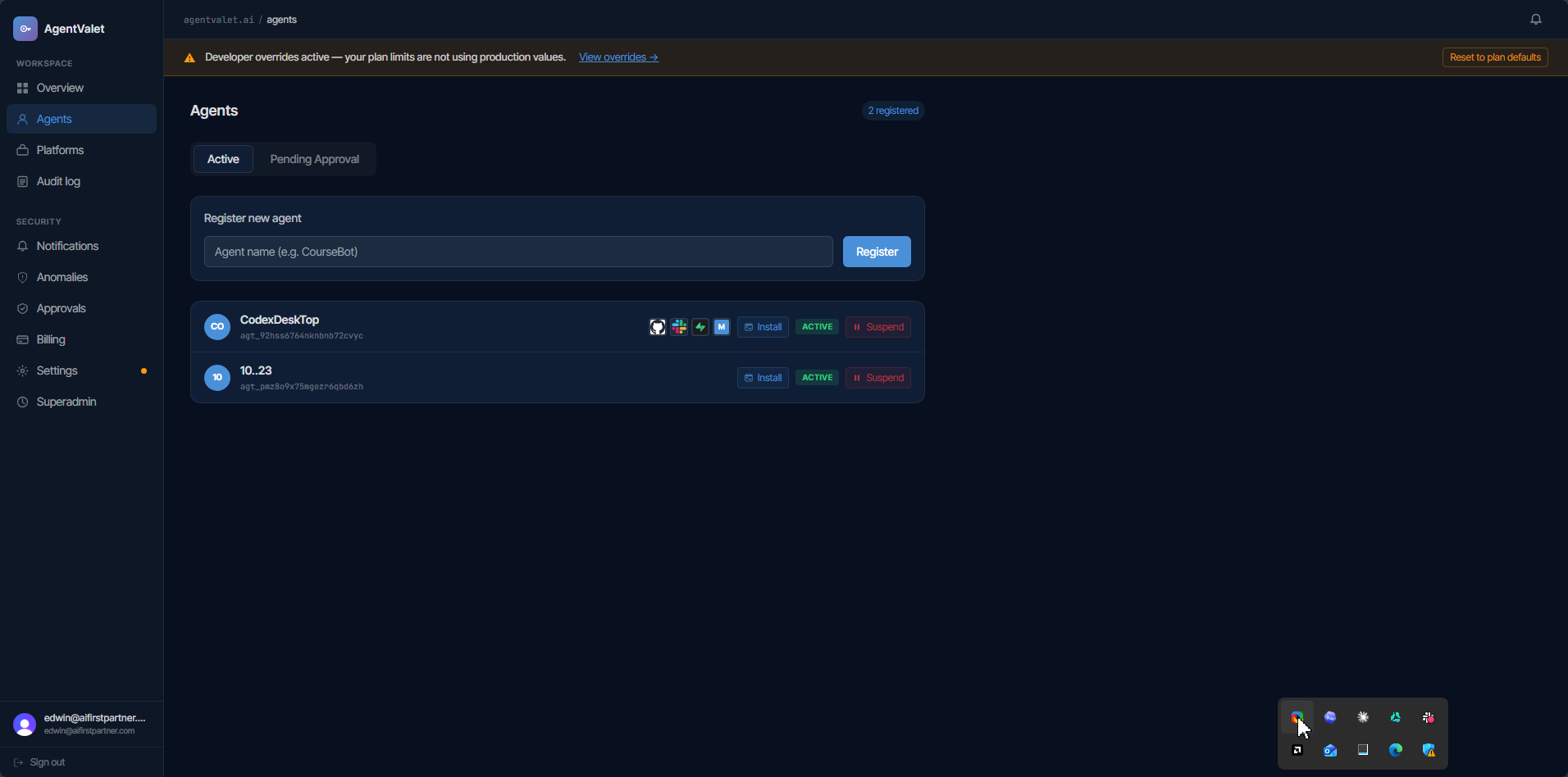
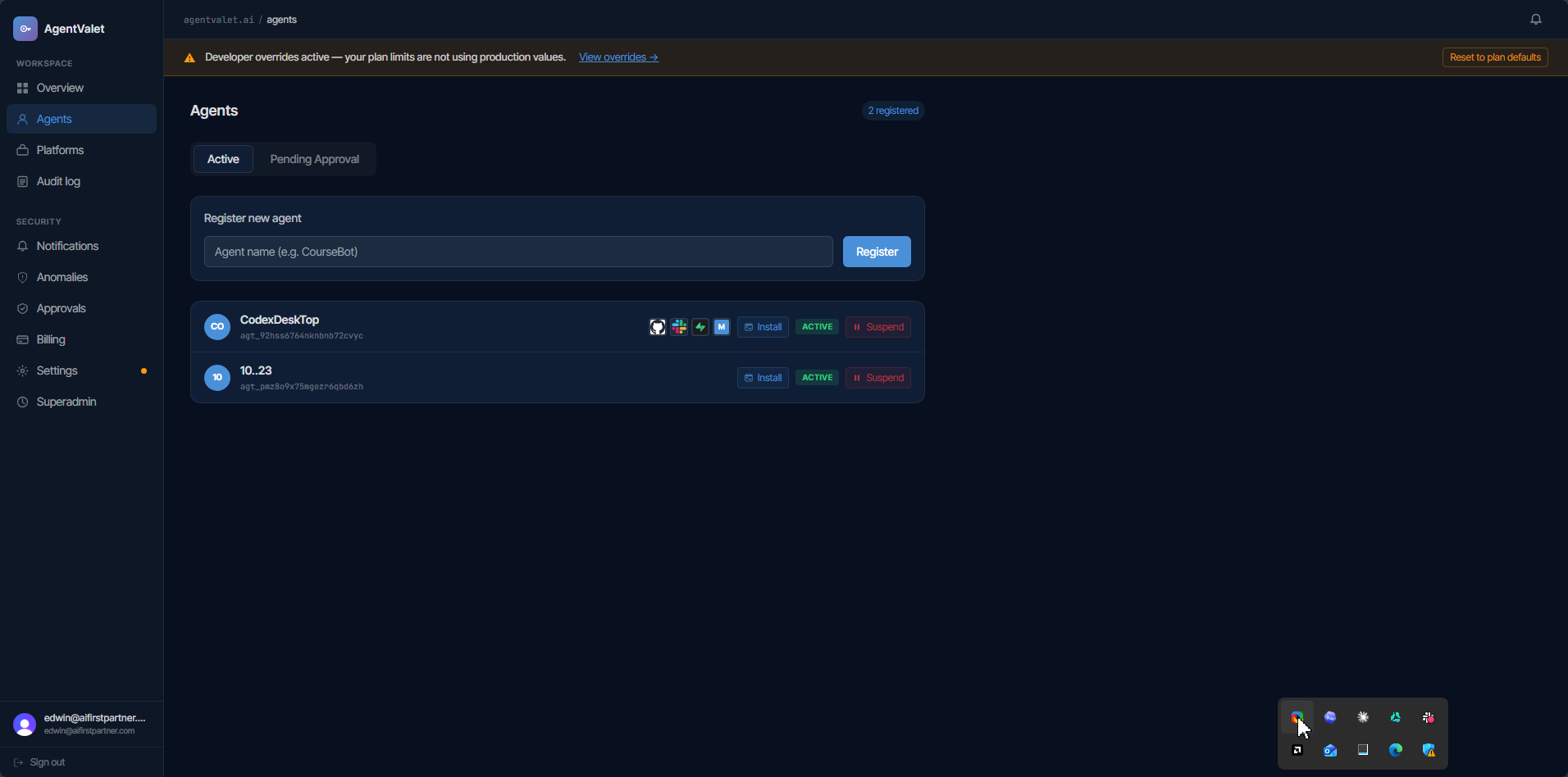
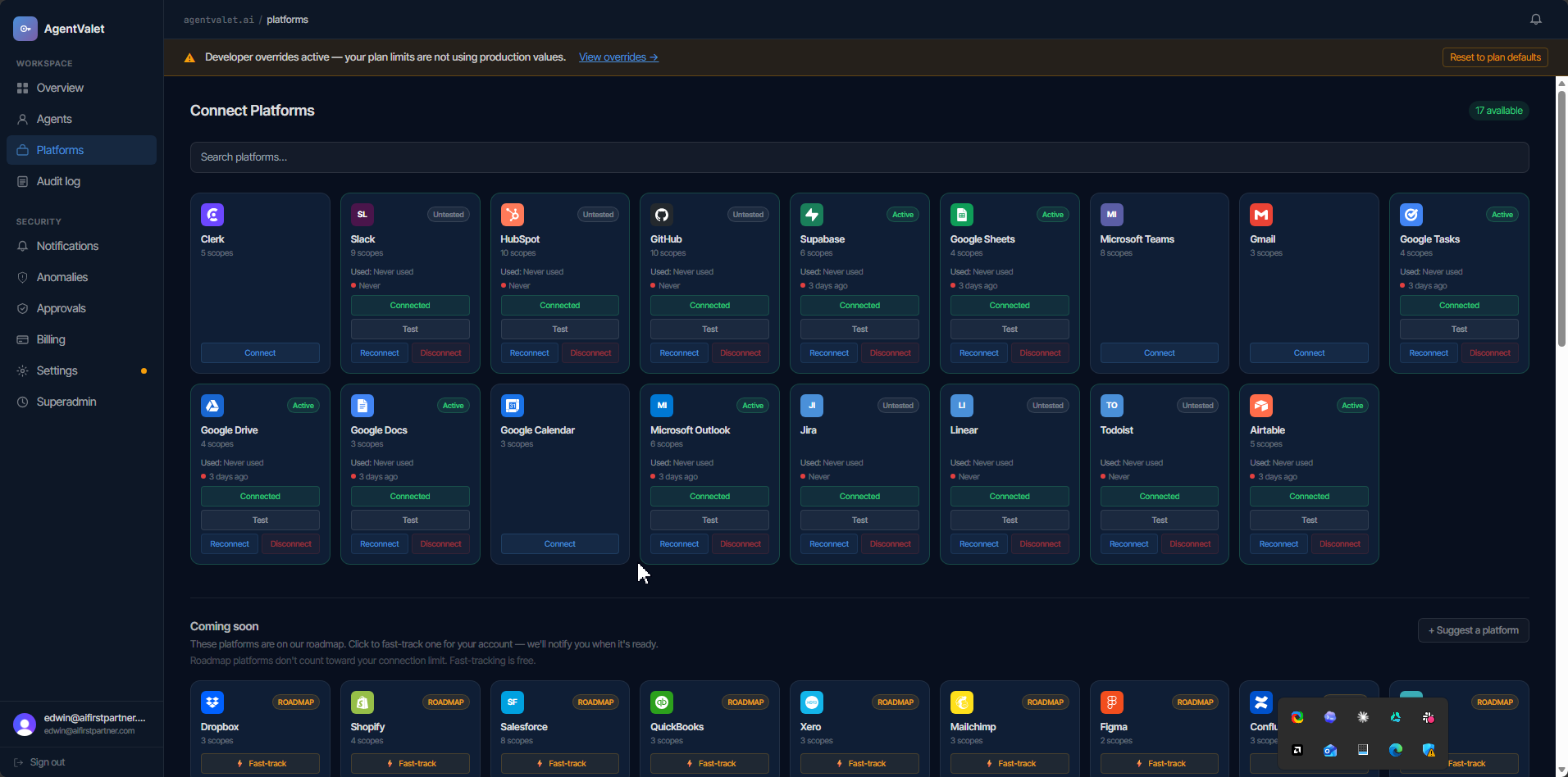
AgentValet is the governance layer for AI agents. It sits between your agents and the 25+ platforms they call — scoped credentials, human approval on the risky stuff, and a full audit trail. One revoke kills access instantly. Live in under 5 minutes, free, no card.
Free tier, no card. Live in under 5 minutes, or we'll wire your first agent with you on a call. 30-day money-back on paid plans.
Read the source on GitHub · Browse the docs · No signup to look
A valet key starts the car and unlocks the driver's door. It won't open the trunk, the glovebox, or the front gate at home. AgentValet hands your AI agent the valet key - and keeps the rest on your hook.
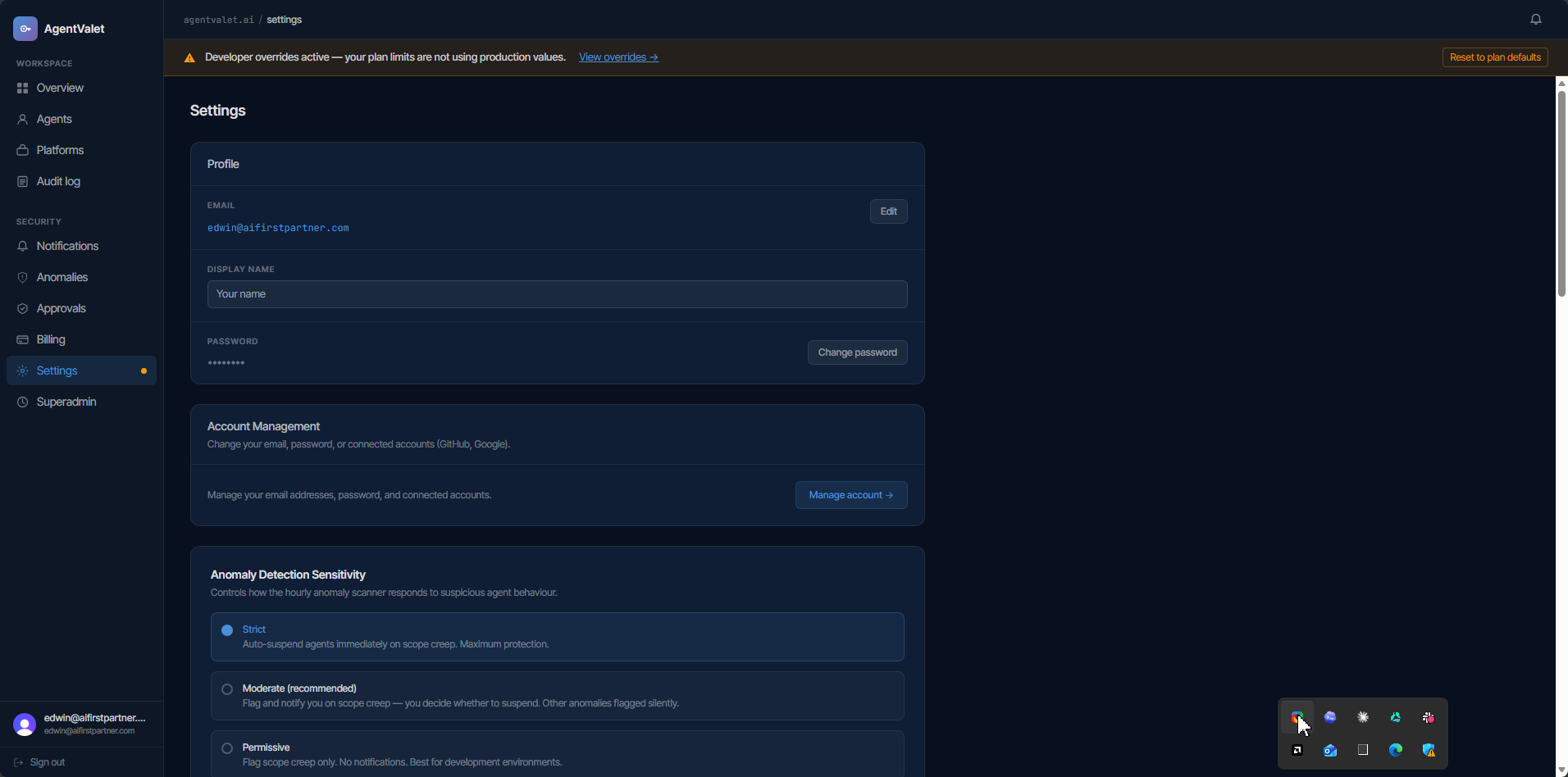
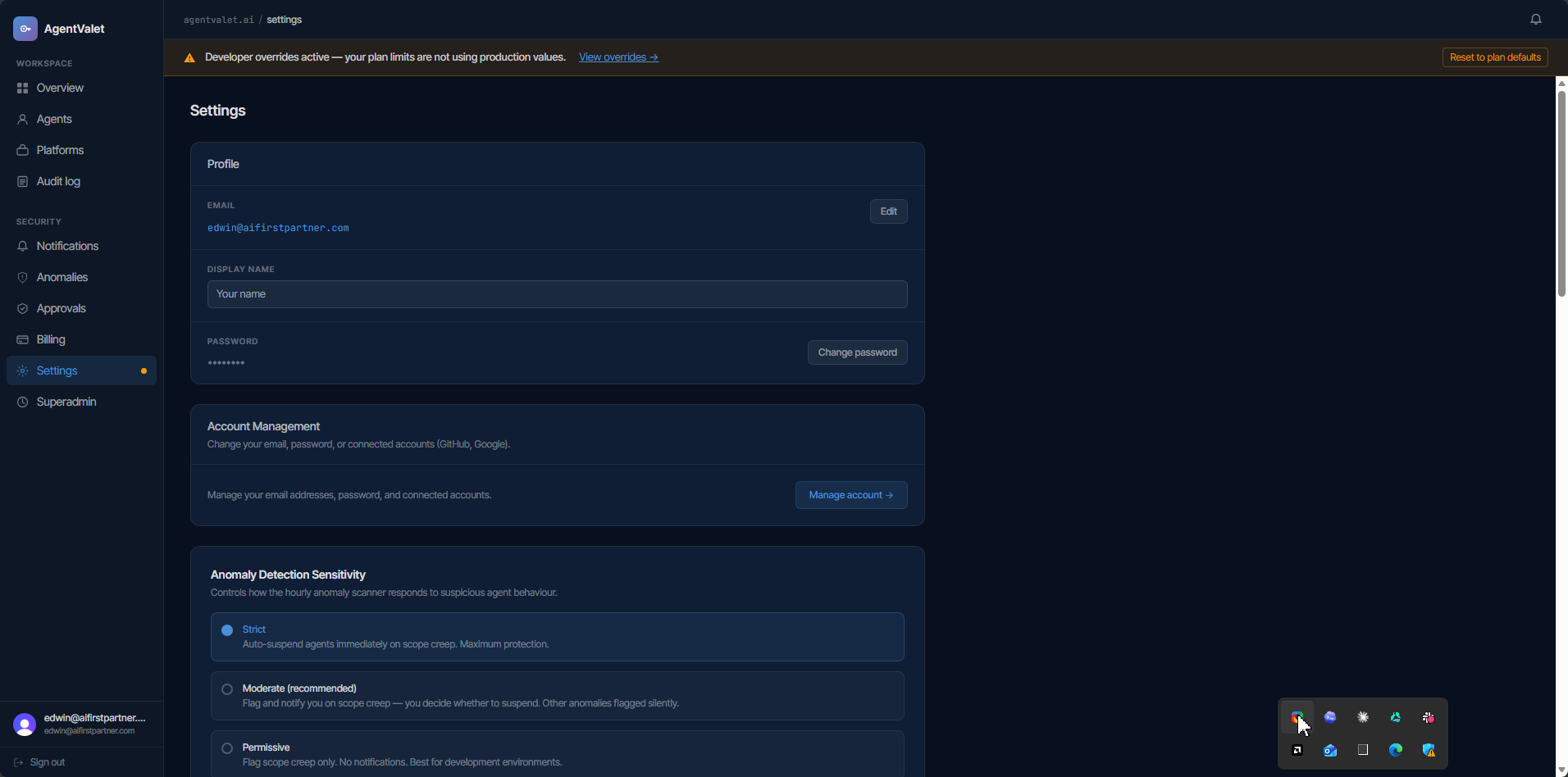
A leaked .env file isn't enough. A compromised laptop isn't enough. A rogue agent isn't enough. Each layer below is independent — an attacker has to defeat all four to reach a live credential.
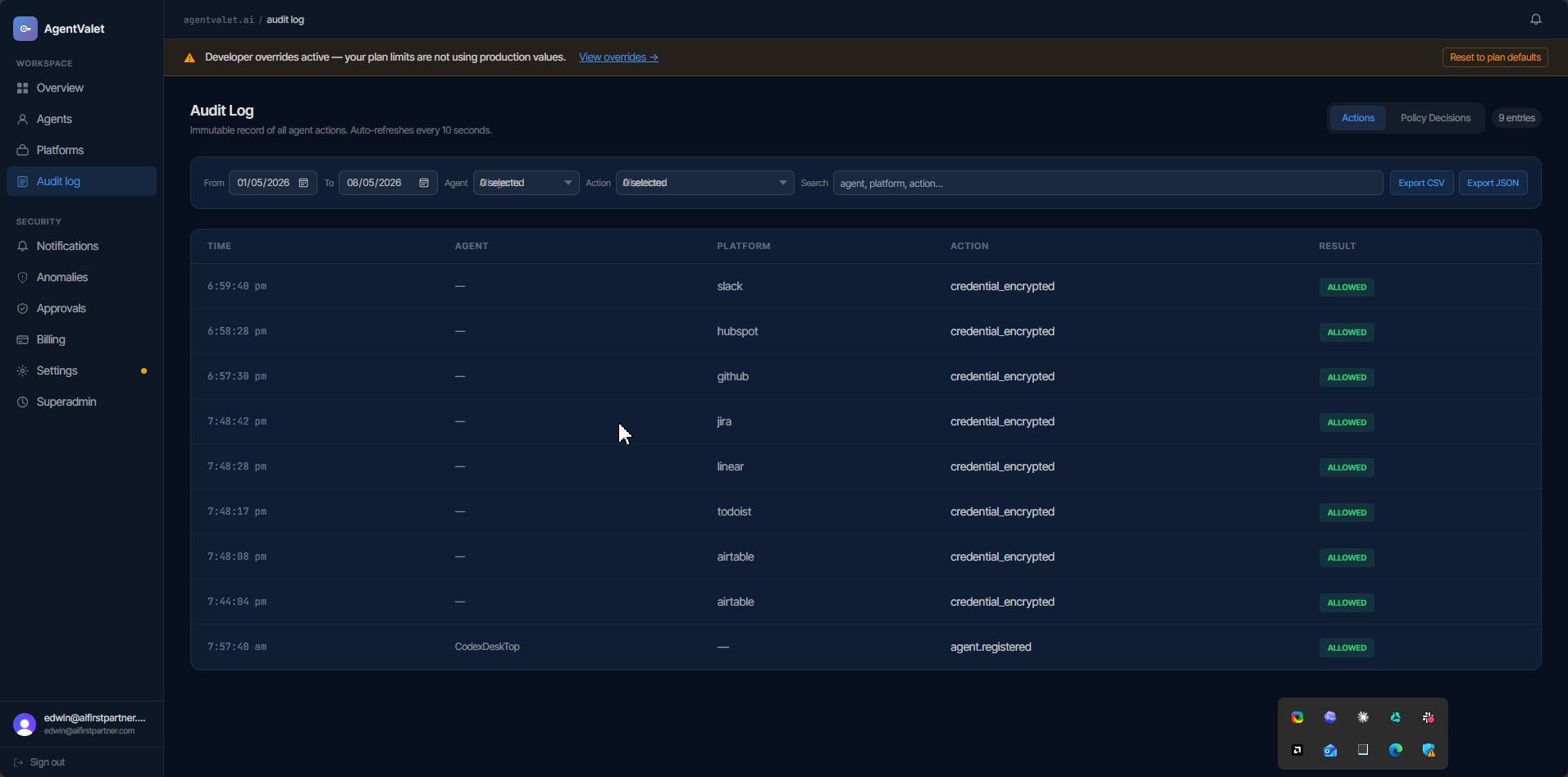
A single console for identity, permissions, platforms, and the audit trail. Built for owners who need to know - and prove - what every agent did.
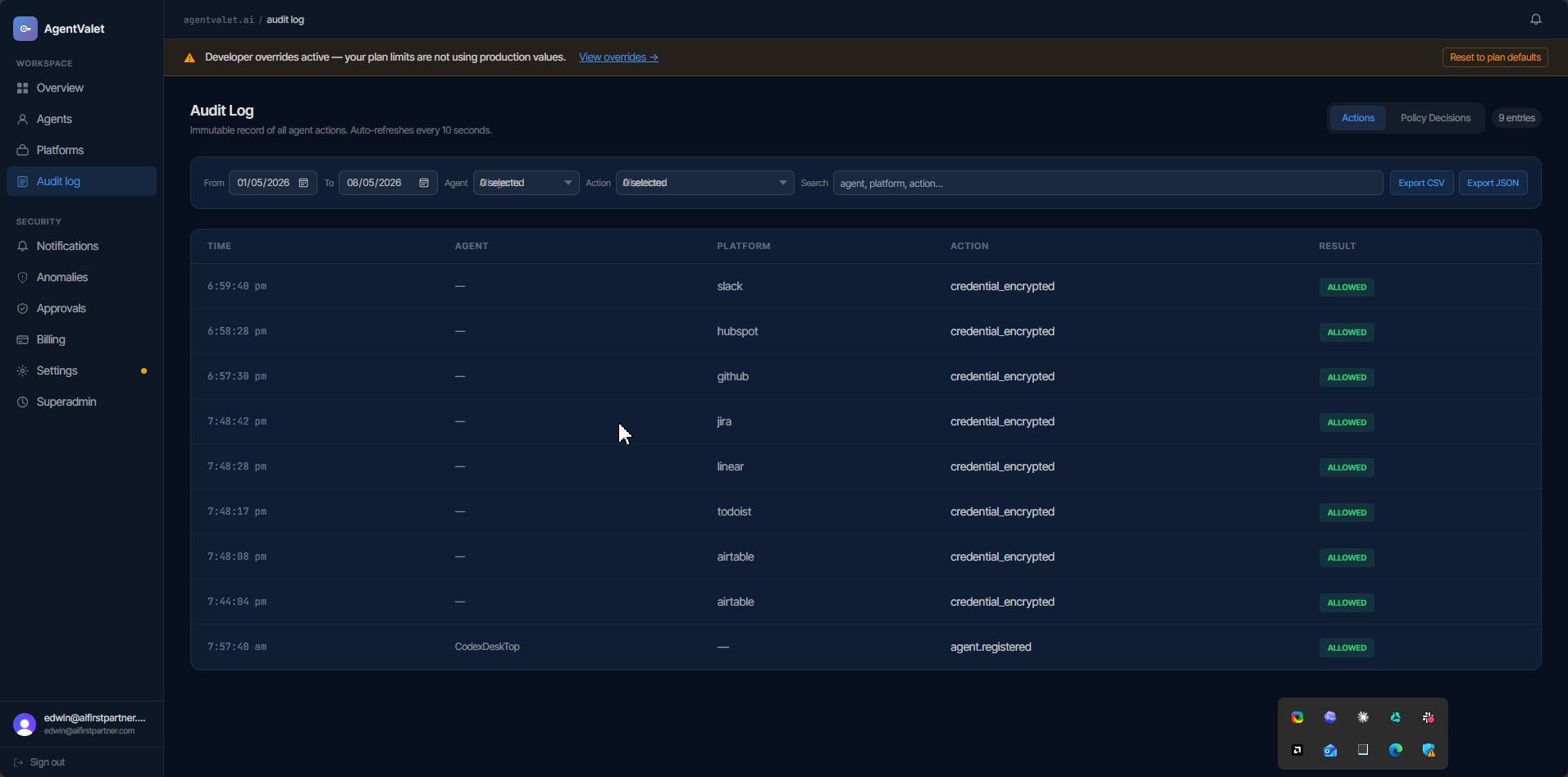
No credential ever touches a log. Six layers stand between your secrets and anything that goes wrong.
A credential broker you can't inspect is just another black box holding your keys. AgentValet is open source, so you can read exactly how credentials are sealed, when they are decrypted, and what gets logged. No signup to look.
Same identity, scope, approval, and audit - whether it's one agent on one machine or fifty across a small team.
AgentValet is in beta. Early-adopter pricing goes up at GA - sign up now and your rate is locked for life.
A separate scoped identity per client, instant offboarding the day an engagement ends, and an isolation trail each client's auditor will accept. Everything in Team, scaled to your whole book of clients.
One stolen key can drain a Stripe account or dump a customer database. With AgentValet, four independent layers have to fail first. Our promise: your first governed agent running in under 5 minutes, or we get on a call and wire it with you. If it isn't keeping live keys off your agents within 30 days, every paid plan is fully refundable. The free tier costs nothing to prove it first.
Your agents never stop mid-run. If you use more calls than your plan includes, we track the extra calls and add them to your next invoice at your plan's overage rate. You'll see the running total in your dashboard, and we'll email you before your bill grows significantly. No surprises. No cutoffs. Pay for what you use.
Hold your own master key in a Key Vault you control, or let us handle the ops while you build.
One MCP endpoint. Connect it to Claude Code, Cursor, Codex CLI, Factory Droid, or Paperclip in minutes. Every agent gets cryptographic identity, scoped credentials, and a full audit trail - no matter which tool is running it.
.cursor/mcp.json - agent-mode tools governed from day one.npx @agentvalet/register wires .mcp.json and CLAUDE.md for you.agentvalet server into claude_desktop_config.json.codex mcp add or drop into .codex/config.toml.droid mcp add or .factory/mcp.json.~/.openclaw/openclaw.json.npx @agentvalet/register automatically injects the correct CLAUDE.md configuration and hooks. Any agent that can make HTTP requests can use the proxy.Deploy in 5 minutes. 30-day money-back guarantee. Cancel any time.
Want to hold your own key? Get notified when BYOK ships →